Tempesta FW
Tempesta® FW is a high-performance secure web edge built into the Linux kernel.
It combines HTTPS load balancing, web acceleration, DDoS mitigation, and WAF capabilities in a single in-kernel data plane.
Unlike conventional user-space proxies and security layers, Tempesta FW processes traffic earlier in the stack. Through its integration with Netfilter, it can enforce filtering logic from L3 to L7. This allows it to block malicious traffic efficiently while improving latency and throughput for legitimate requests.
The result is a platform that helps protect web applications without adding the usual security overhead.
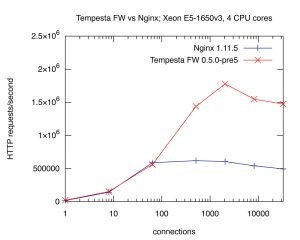
Tempesta FW services up to 1.8M HTTP requests per second on the cheapest hardware. The benchmark results are open and easily reproducible.
Full-Stack DDoS and Bot Protection
Tempesta FW can be integrated with Tempesta xFW and Tempesta WebShield to provide full-stack protection against volumetric L3/L4 attacks, application-layer L7 DDoS, and advanced bot activity. Tempesta FW handles application-layer filtering in the Linux kernel, Tempesta xFW mitigates volumetric attacks early in the packet path, and Tempesta WebShield detects abusive automation from real traffic behavior.
Application Security
We developed the fastest HTTP parser technology , which allows Tempesta FW not only process millions HTTP requests per second, but also do thousands of security checks right during HTTP parsing. Various injection attacks, including XSS and SQL injections, password crackers, HTTP requests smuggling and response splitting, cache poisoning and many others are filtered out at a speed larger than traditional web accelerators can parse HTTP messages.
Web Acceleration
Tempesta FW uses a very fast ultra-scalable in-memory database Tempesta DB to handle a web cache.
Load Balancing
Tempesta FW provides a rich set of load balancing strategies such as persistent sessions, complex conditional statements over almost any set of HTTP request fields, weighted round-robin, rendezvous hashing, etc. Tempesta FW also uses machine learning to dynamically learn and predict changes in the performance and the availability of each of your backend servers, so there is no need to configure and maintain many different weights in your web cluster!
Application Performance Monitoring
Tempesta FW dynamically monitors upstream server performance and provides a comprehensive set of performance metrics. Application availability can be monitored using passive or active health monitoring techniques. Load balancing logic is integrated with the health and performance monitoring and dynamically changes traffic distribution among the upstream servers.
HTTP Tables
HTTP tables is an extension of standard Linux iptables, nftables and/or bpfilter for the network application layer, HTTP(S) protocol in particular. You can write multi-layer network filtration rules using Tempesta FW HTTP tables, e.g. filter all HTTP requests from a particular IP with a particular HTTP header. Learn more about HTTP tables in our knowledge base.
TLS Termination
Tempesta TLS extends the Linux TCP/IP stack with the TLS protocol, so it avoids context switches unavoidable for traditional user space libraries and constructs TLS records in the most efficient way using the current TCP state data. Tempesta TLS also employs the modern asymmetric cryptography research and advanced zero-copy techniques. This all allows Tempesta FW to establish x2 more handshakes with x4 lower latency than Nginx using OpenSSL or WolfSSL libraries. TLS handshakes rate limiting efficiently mitigates TLS handshakes DDoS attacks.
Performance
Tempesta FW is designed to deliver the highest performance in HTTP processing under various workloads. High performance servicing of unusual traffic is crucial for resistance against complex DDoS attacks, including targeted DDoS attacks. Most types of HTTP floods can be mitigated without any configuration effort thanks to the fast processing engine.
How It Works
Tempesta FW is embedded into the Linux TCP/IP stack and works in the kernel space, but administered from the user space just like any traditional web accelerators.
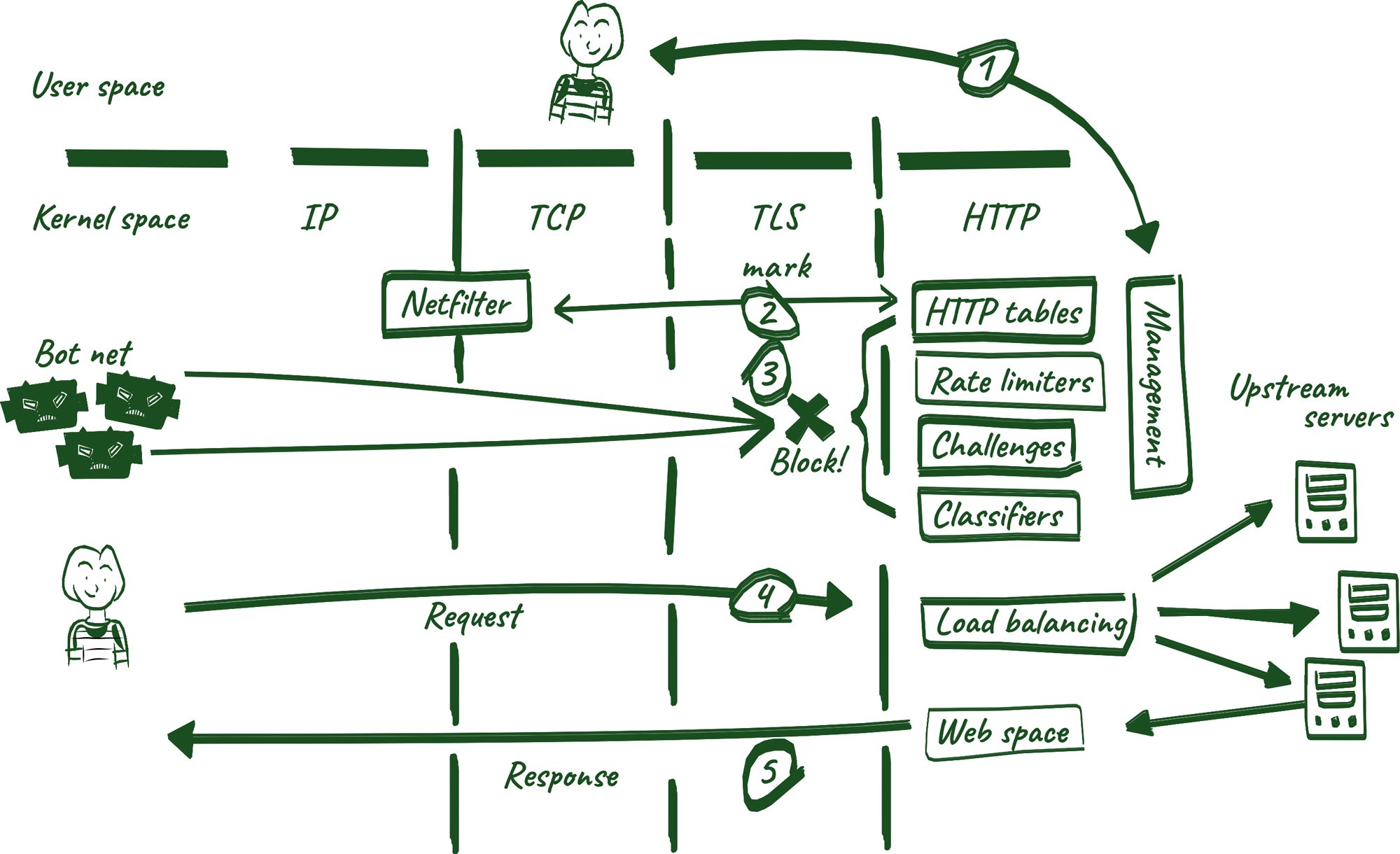
- An administrator starts, stops and configure Tempesta FW just like any traditional user space HTTP accelerator.
- HTTP tables and the Linux firewall engine Netfilter communicate using packets marking to express multi-layer network filtering rules.
- DDoS attack, web attacks and bots are blocked by the HTTP tables and rate limiting rules, JavaScript and cookie challenges and dynamic classification logic.
- Normal user requests are load balanced among upstream servers.
- Server responses are stored in the web cache and returned to the user.
Deployment

High availability The reliability of a web cluster is extremely important. Please check the Wiki page for scenarios of highly available Tempesta FW installations.

Clouds Tempesta FW can be deployed in clouds as well as on bare metal. You can learn more about cloud installation in our Wiki.

Installation You can install Tempesta FW from sources or prebuilt packages. System requirements can be found on our Wiki.
Commercial Support

Tempesta FW online documentation is available in the knowledge base.

We can help you to install and configure Tempesta FW as well as to tune your operating system to ensure maximum performance. Our experts have years of experience in high-performance network traffic processing and databases, including both the development and management sides. We’d be happy to help you build a high-performance, scalable, and highly available system using Tempesta FW.

Please contact us for any inquiries.