DDoS Protection
At Scale, Cloud Protection and Appliances Become Limiting Factors
You Need DDoS Protection You Control
Cost – cloud protection and appliances become prohibitively expensive at high traffic volumes
Dependency – availability depends on external providers and their decisions
Inflexibility – targeted attacks demand custom protection logic for specific applications
Big vendors = big targets – attackers bypass Cloudflare, Akamai & Ko to attack big companies, so all others are exposed at once
Compliance – regulated environments cannot pass traffic through third parties
No vendor lock-in.
No black-box logic.
Full control.
eBPF-based Volumetric DDoS Protection
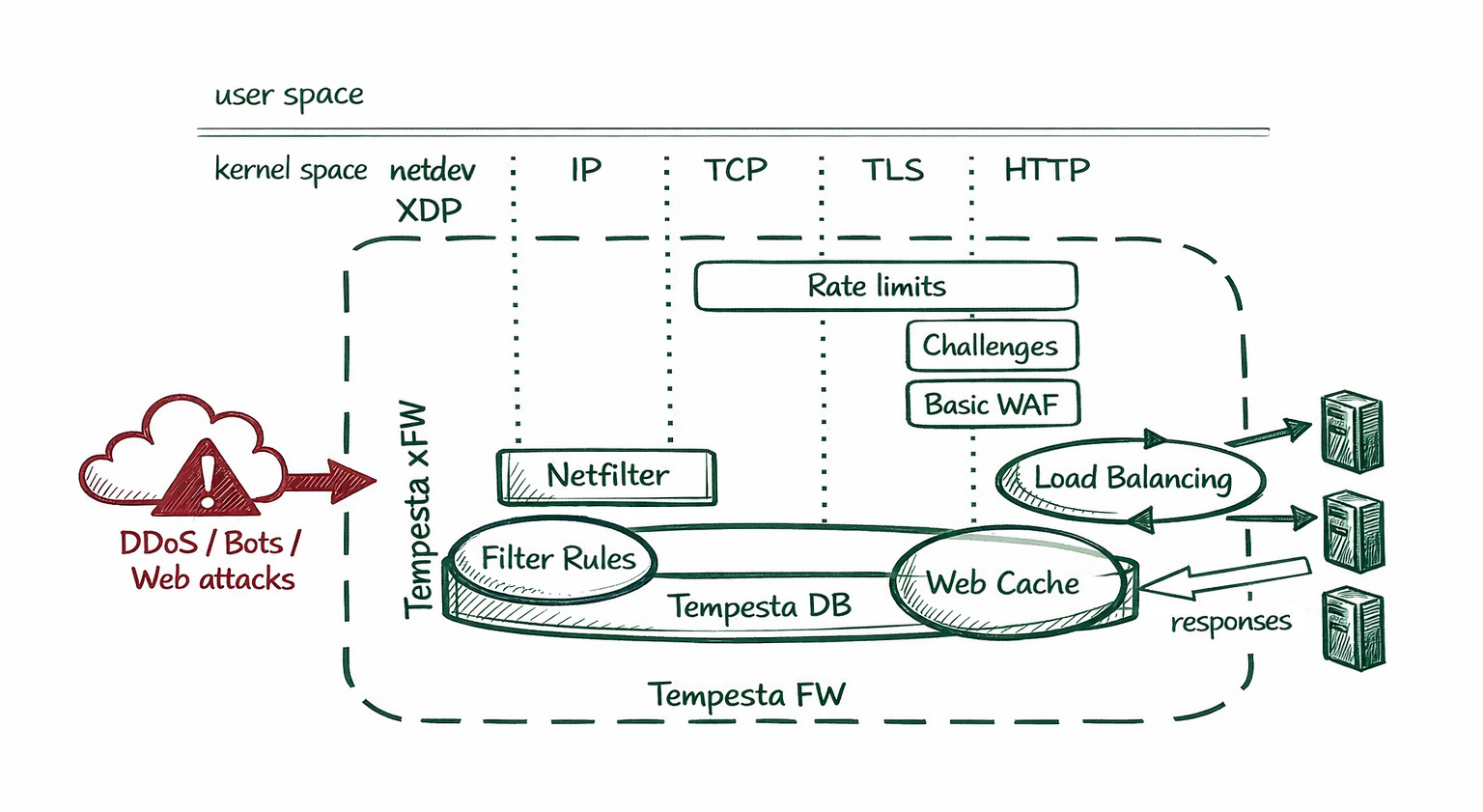
Tempesta xFW is open-source suite of Linux XDP and TC eBPF modules for volumetric DDoS protection. Its layered filtering architecture efficiently blocks both large-scale volumetric attacks and hybrid attacks.
Deployment Architectures
Tempesta xFW can be deployed either in pass-through (inline) mode or in redirection (out-of-path) mode. It can operate as always-on or on-demand scenarios. In on-demand and/or redirection deployments, it can be integrated with a DDoS detection sensor.
L3-L7 Protection
Tempesta xFW supports filtering DDoS attacks across all network layers:
- IPv4, IPv6, ICMPv4, ICMPv6,
- TCP, UDP, GRE
- DNS
- HTTPS, HTTP/2 (with Tempesta FW)
DNS Protection
Tempesta xFW protects DNS servers against DNS attacks, including DNS and UDP floods, and also prevents them from being abused as reflectors in reflection and amplification attacks.
Web and API Protection
Protection of web resources using HTTPS, HTTP/2 and HTTP/3 (QUIC) against TCP and UDP floods. Tempesta FW can be deployed on the same host as an already running web server or proxy. It automatically learns active TCP flows and blocks garbage packets unrelated to known or newly established legitimate TCP flows.
Observability
Traffic counters are exported in Prometheus format for seamless integration with monitoring solutions.
All blocking events can be written to ClickHouse database using efficient zero-copy transport.
Host and Network Protection
Tempesta xFW supports both host and gateway deployment modes.
In host mode, it runs on the same machine as the protected web, DNS or other service. The typical use cases are an HTTP load balancer and a DNS server.
In gateway mode, it runs as a Linux router protecting entire networks. The typical use cases are ISP scrubbing and corporate network protection.
Automatic Incident Reporting
Tempesta Escudo is the commercial edition of Tempesta xFW. It includes automatic incident reporting allowing our team to be notified in Slack as soon as an incident occurs on one of your servers.
No support tickets or emails are required. The relevant diagnostic data is collected automatically, so we can start investigating immediately.
Data collection scripts are shipped as source code, so you remain in control of what information is shared externally.

Full-Stack DDoS and Bot Protection
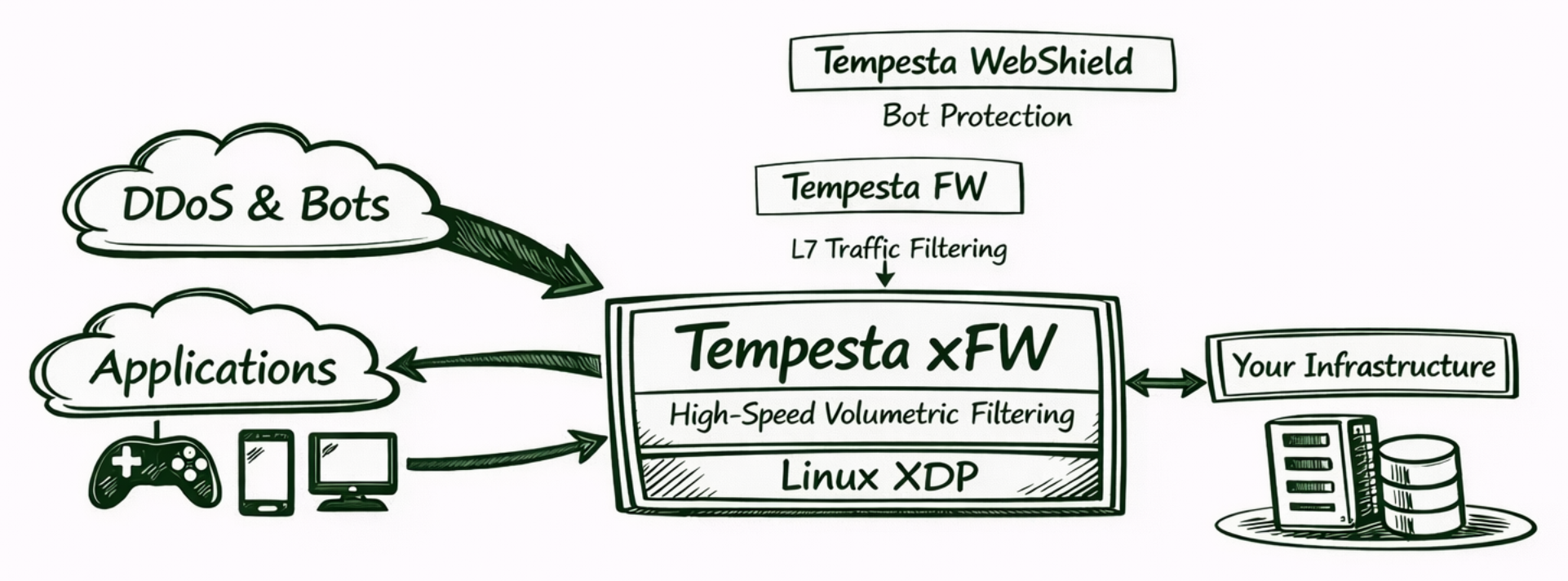
Tempesta xFW can be integrated with Tempesta FW and Tempesta WebShield to provide full-stack protection against volumetric L3/L4 attacks, application-layer L7 DDoS attacks, and unwanted bots.
Tempesta WebShield analyzes Tempesta FW access logs to learn normal user behavior and detect web scrapers, carting and checkout abuse, inventory scraping, security scanning, L7 DDoS attacks, and other advanced bot activity.
Watch our FOSDEM’26 talk to learn more.
Deployment

Evaluation mode provides a safe way to assess system behavior and mitigation effectiveness on production traffic without affecting legitimate user traffic.

Tempesta xFW can be deployed in cloud environments, including Docker and Kubernetes, as well as on bare metal and virtual machines, including KVM-based deployments.

Tempesta xFW can be installed from prebuilt packages. System requirements are available in our Wiki.
Commercial Support and Custom Development
Our team provides commercial support and custom development services for Tempesta xFW, FW and WebShield:

Aarchitecture and performance review, plus consulting on securing target applications

Deployment design and assistance with Tempesta xFW installation and configuration on your servers

incident analysis and real-time support during attacks

custom extensions for specific environments and workloads, such as gaming, available under commercial terms

Please contact us for any inquiries.

